<xsd:element name="fileauditedpermissions_object" substitutionGroup="oval-def:object">
<xsd:annotation>
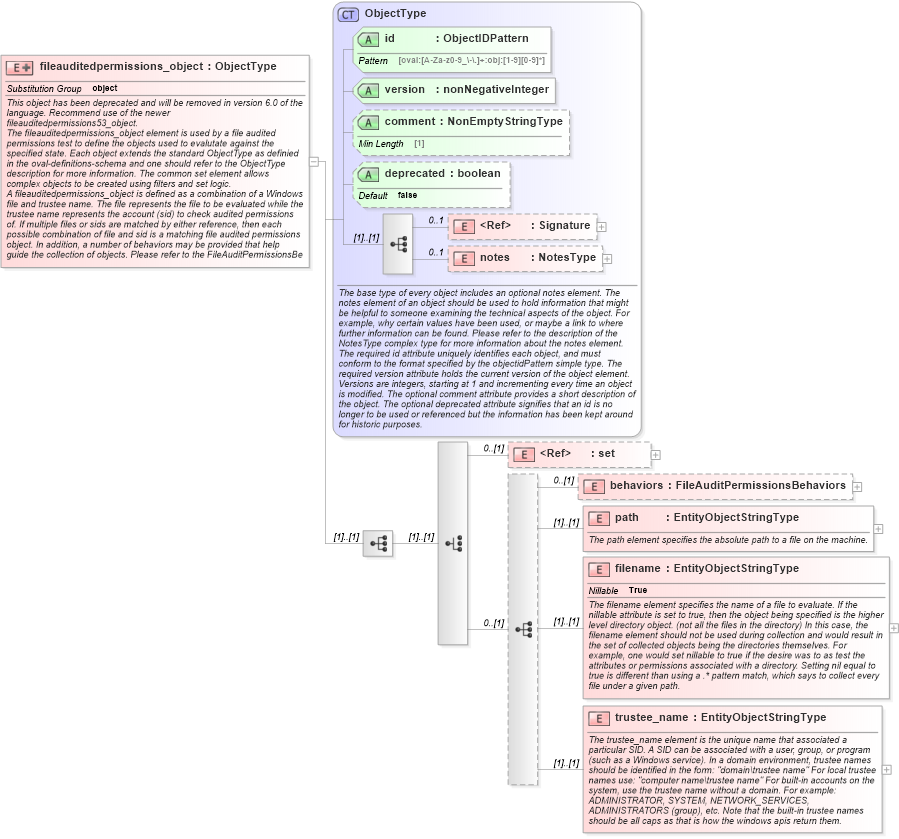
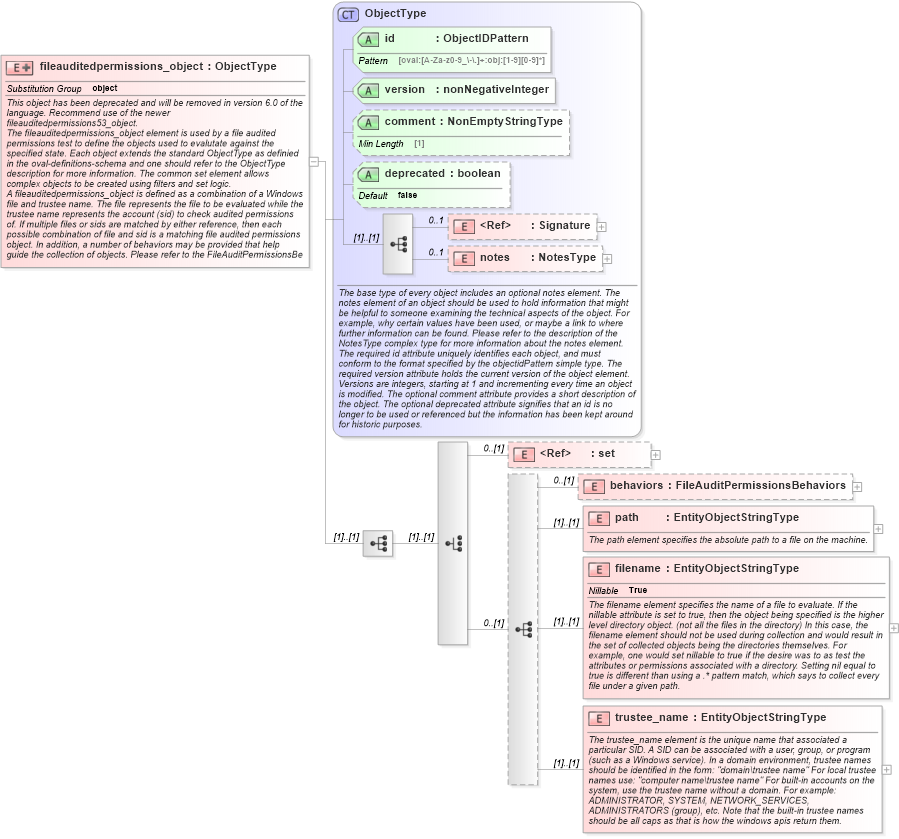
<xsd:documentation>This object has been deprecated and will be removed in version 6.0 of the language. Recommend use of the newer fileauditedpermissions53_object.</xsd:documentation>
<xsd:documentation>The fileauditedpermissions_object element is used by a file audited permissions test to define the objects used to evalutate against the specified state. Each object extends the standard ObjectType as definied in the oval-definitions-schema and one should refer to the ObjectType description for more information. The common set element allows complex objects to be created using filters and set logic.</xsd:documentation>
<xsd:documentation>A fileauditedpermissions_object is defined as a combination of a Windows file and trustee name. The file represents the file to be evaluated while the trustee name represents the account (sid) to check audited permissions of. If multiple files or sids are matched by either reference, then each possible combination of file and sid is a matching file audited permissions object. In addition, a number of behaviors may be provided that help guide the collection of objects. Please refer to the FileAuditPermissionsBehaviors complex type for more information about specific behaviors.</xsd:documentation>
</xsd:annotation>
<xsd:complexType>
<xsd:complexContent>
<xsd:extension base="oval-def:ObjectType">
<xsd:sequence>
<xsd:choice>
<xsd:element ref="oval-def:set" minOccurs="0" />
<xsd:sequence minOccurs="0">
<xsd:element name="behaviors" type="win-def:FileAuditPermissionsBehaviors" minOccurs="0" />
<xsd:element name="path" type="oval-def:EntityObjectStringType">
<xsd:annotation>
<xsd:documentation>The path element specifies the absolute path to a file on the machine.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="fapobjpath" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:fileauditedpermissions_object/win-def:path">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the path entity of a fileauditedpermissions_object should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="filename" type="oval-def:EntityObjectStringType" nillable="true">
<xsd:annotation>
<xsd:documentation>The filename element specifies the name of a file to evaluate. If the nillable attribute is set to true, then the object being specified is the higher level directory object. (not all the files in the directory) In this case, the filename element should not be used during collection and would result in the set of collected objects being the directories themselves. For example, one would set nillable to true if the desire was to as test the attributes or permissions associated with a directory. Setting nil equal to true is different than using a .* pattern match, which says to collect every file under a given path.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="fapobjfilename" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:fileauditedpermissions_object/win-def:filename">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the filename entity of a fileauditedpermissions_object should be 'string'</sch:assert>
<sch:assert test="if (not(@operation) or @operation='equals' or @operation='not equal') then (not(contains(.,'\') or contains(.,'/') or contains(.,':') or contains(.,'*') or contains(.,'?') or contains(.,'>') or contains(.,'|'))) else (1=1)">
<sch:value-of select="../@id" /> - filename entity can not contain the characters / \ : * ? > | </sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="trustee_name" type="oval-def:EntityObjectStringType">
<xsd:annotation>
<xsd:documentation>The trustee_name element is the unique name that associated a particular SID. A SID can be associated with a user, group, or program (such as a Windows service). In a domain environment, trustee names should be identified in the form: "domain\trustee name" For local trustee names use: "computer name\trustee name" For built-in accounts on the system, use the trustee name without a domain. For example: ADMINISTRATOR, SYSTEM, NETWORK_SERVICES, ADMINISTRATORS (group), etc. Note that the built-in trustee names should be all caps as that is how the windows apis return them.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="fapobjtrustee_name" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:fileauditedpermissions_object/win-def:trustee_name">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the trustee_name entity of a fileauditedpermissions_object should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
</xsd:sequence>
</xsd:choice>
</xsd:sequence>
</xsd:extension>
</xsd:complexContent>
</xsd:complexType>
</xsd:element>
|