<xsd:element name="regkeyauditedpermissions53_object" substitutionGroup="oval-def:object">
<xsd:annotation>
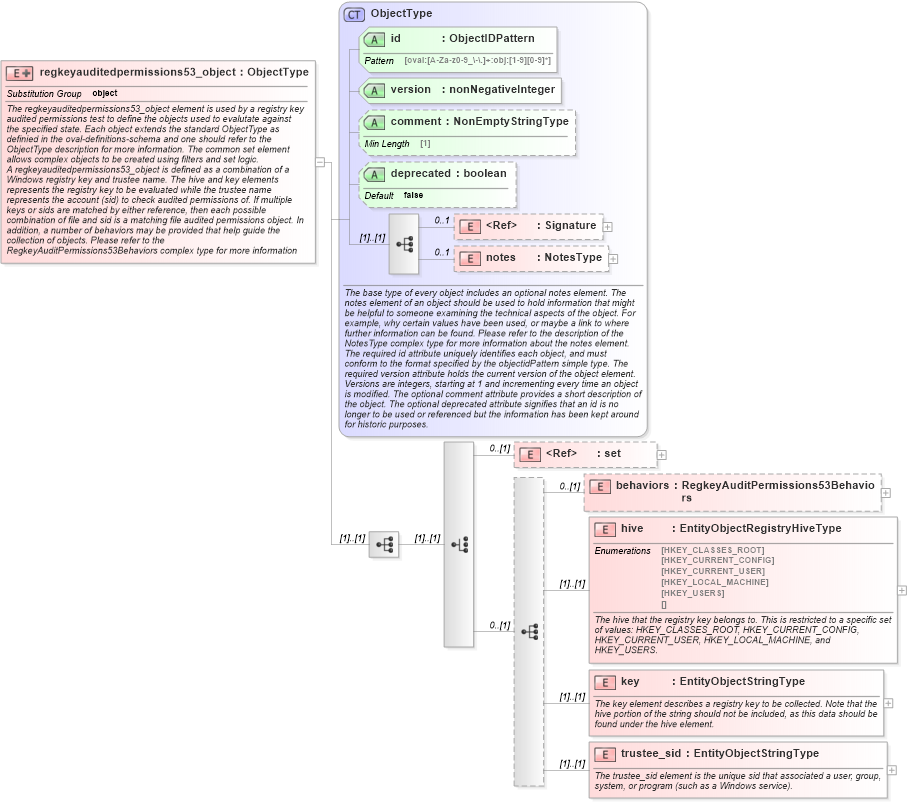
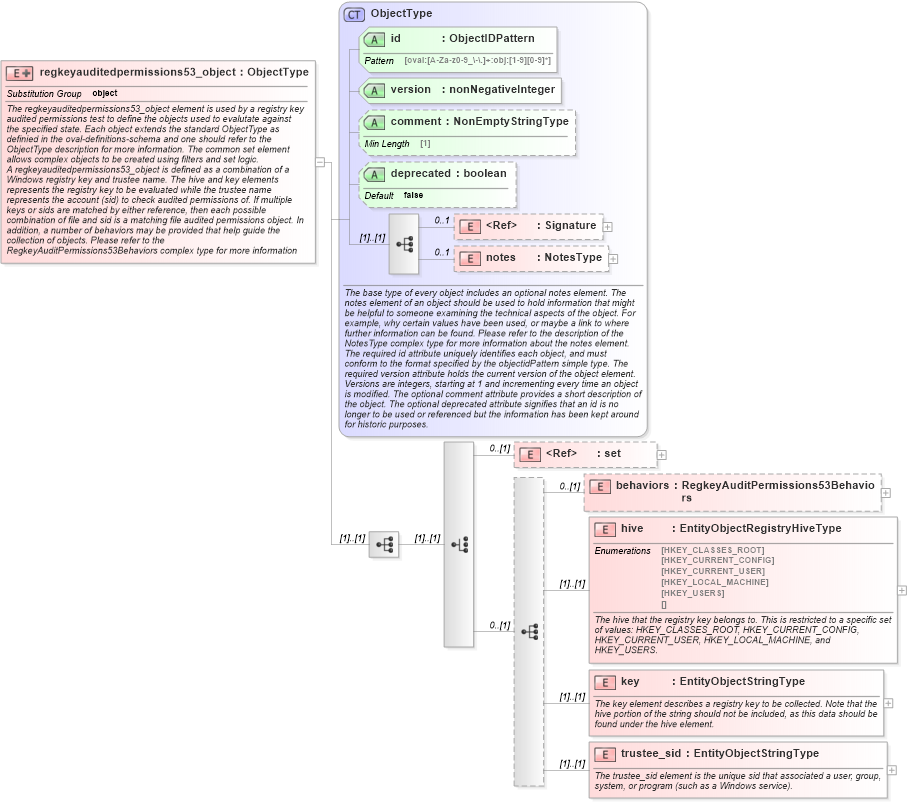
<xsd:documentation>The regkeyauditedpermissions53_object element is used by a registry key audited permissions test to define the objects used to evalutate against the specified state. Each object extends the standard ObjectType as definied in the oval-definitions-schema and one should refer to the ObjectType description for more information. The common set element allows complex objects to be created using filters and set logic.</xsd:documentation>
<xsd:documentation>A regkeyauditedpermissions53_object is defined as a combination of a Windows registry key and trustee name. The hive and key elements represents the registry key to be evaluated while the trustee name represents the account (sid) to check audited permissions of. If multiple keys or sids are matched by either reference, then each possible combination of file and sid is a matching file audited permissions object. In addition, a number of behaviors may be provided that help guide the collection of objects. Please refer to the RegkeyAuditPermissions53Behaviors complex type for more information about specific behaviors.</xsd:documentation>
</xsd:annotation>
<xsd:complexType>
<xsd:complexContent>
<xsd:extension base="oval-def:ObjectType">
<xsd:sequence>
<xsd:choice>
<xsd:element ref="oval-def:set" minOccurs="0" />
<xsd:sequence minOccurs="0">
<xsd:element name="behaviors" type="win-def:RegkeyAuditPermissions53Behaviors" minOccurs="0" />
<xsd:element name="hive" type="win-def:EntityObjectRegistryHiveType">
<xsd:annotation>
<xsd:documentation>The hive that the registry key belongs to. This is restricted to a specific set of values: HKEY_CLASSES_ROOT, HKEY_CURRENT_CONFIG, HKEY_CURRENT_USER, HKEY_LOCAL_MACHINE, and HKEY_USERS.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="rap53objhive" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:regkeyauditedpermissions53_object/win-def:hive">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the hive entity of a regkeyauditedpermissions53_object should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="key" type="oval-def:EntityObjectStringType">
<xsd:annotation>
<xsd:documentation>The key element describes a registry key to be collected. Note that the hive portion of the string should not be included, as this data should be found under the hive element.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="rap53objkey" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:regkeyauditedpermissions53_object/win-def:key">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the key entity of a regkeyauditedpermissions53_object should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="trustee_sid" type="oval-def:EntityObjectStringType">
<xsd:annotation>
<xsd:documentation>The trustee_sid element is the unique sid that associated a user, group, system, or program (such as a Windows service).</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="rap53objtrustee_sid" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-def:regkeyauditedpermissions53_object/win-def:trustee_sid">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the trustee_sid entity of a regkeyauditedpermissions53_object should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
</xsd:sequence>
</xsd:choice>
</xsd:sequence>
</xsd:extension>
</xsd:complexContent>
</xsd:complexType>
</xsd:element>
|