<xsd:element name="auditeventpolicy_item" substitutionGroup="oval-sc:item">
<xsd:annotation>
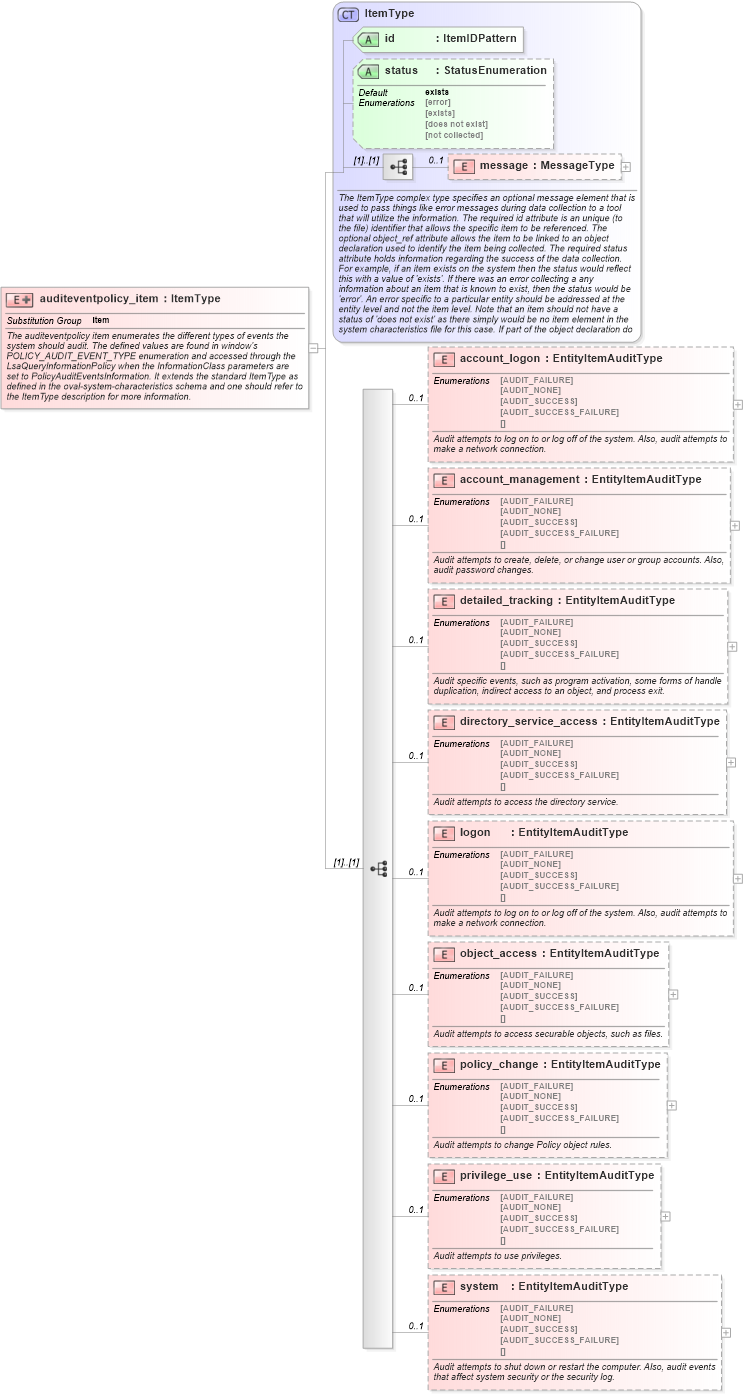
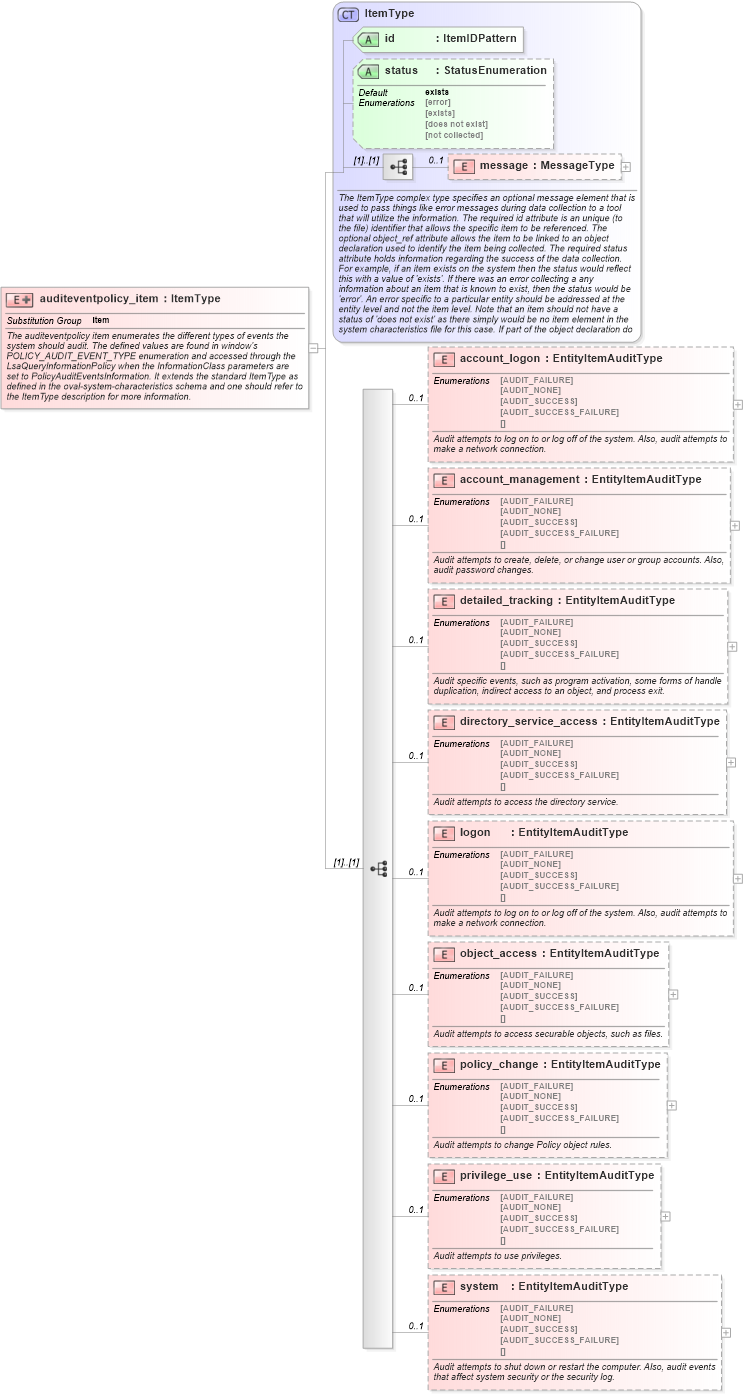
<xsd:documentation>The auditeventpolicy item enumerates the different types of events the system should audit. The defined values are found in window's POLICY_AUDIT_EVENT_TYPE enumeration and accessed through the LsaQueryInformationPolicy when the InformationClass parameters are set to PolicyAuditEventsInformation. It extends the standard ItemType as defined in the oval-system-characteristics schema and one should refer to the ItemType description for more information.</xsd:documentation>
</xsd:annotation>
<xsd:complexType>
<xsd:complexContent>
<xsd:extension base="oval-sc:ItemType">
<xsd:sequence>
<xsd:element name="account_logon" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to log on to or log off of the system. Also, audit attempts to make a network connection.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemaccount_logon" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:account_logon">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the account_logon entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="account_management" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to create, delete, or change user or group accounts. Also, audit password changes.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemaccount_management" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:account_management">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the account_management entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="detailed_tracking" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit specific events, such as program activation, some forms of handle duplication, indirect access to an object, and process exit. </xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemdetailed_tracking" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:detailed_tracking">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the detailed_tracking entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="directory_service_access" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to access the directory service.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemdirectory_service_access" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:directory_service_access">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the directory_service_access entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="logon" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to log on to or log off of the system. Also, audit attempts to make a network connection.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemlogon" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:logon">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the logon entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="object_access" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to access securable objects, such as files.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemobject_access" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:object_access">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the object_access entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="policy_change" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to change Policy object rules. </xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitempolicy_change" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:policy_change">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the policy_change entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="privilege_use" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to use privileges.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemprivilege_use" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:privilege_use">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the privilege_use entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="system" type="win-sc:EntityItemAuditType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Audit attempts to shut down or restart the computer. Also, audit events that affect system security or the security log.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="aepitemsystem" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:auditeventpolicy_item/win-sc:system">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the system entity of an auditeventpolicy_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
</xsd:sequence>
</xsd:extension>
</xsd:complexContent>
</xsd:complexType>
</xsd:element>
|