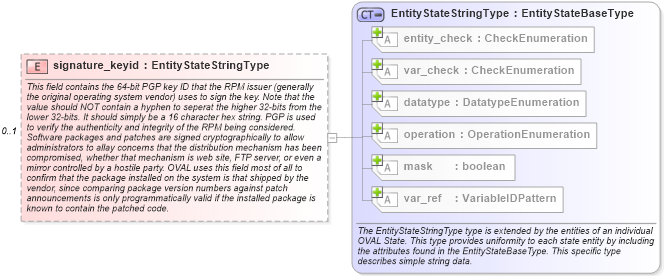
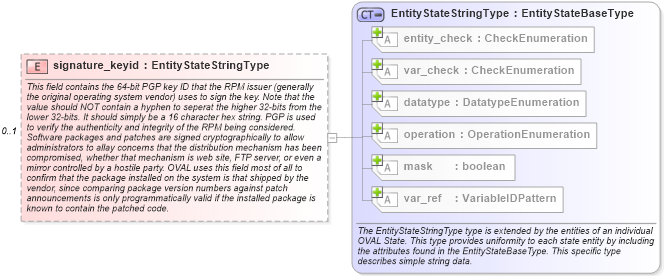
<xsd:element name="signature_keyid" type="oval-def:EntityStateStringType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>This field contains the 64-bit PGP key ID that the RPM issuer (generally the original operating system vendor) uses to sign the key. Note that the value should NOT contain a hyphen to seperat the higher 32-bits from the lower 32-bits. It should simply be a 16 character hex string. PGP is used to verify the authenticity and integrity of the RPM being considered. Software packages and patches are signed cryptographically to allow administrators to allay concerns that the distribution mechanism has been compromised, whether that mechanism is web site, FTP server, or even a mirror controlled by a hostile party. OVAL uses this field most of all to confirm that the package installed on the system is that shipped by the vendor, since comparing package version numbers against patch announcements is only programmatically valid if the installed package is known to contain the patched code.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="rpmstesignaturekeyid" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="linux-def:rpminfo_state/linux-def:signature_keyid">
<sch:assert test="not(@datatype) or @datatype='string'">
<sch:value-of select="../@id" /> - datatype attribute for the signature_keyid entity of a rpminfo_state should be 'string'</sch:assert>
<sch:assert test="not(@operation) or @operation='equals' or @operation='not equal' or @operation='pattern match'">
<sch:value-of select="../@id" /> - operation attribute for the signature_keyid entity of a rpminfo_state should be 'equals', 'not equal', or 'pattern match'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
|