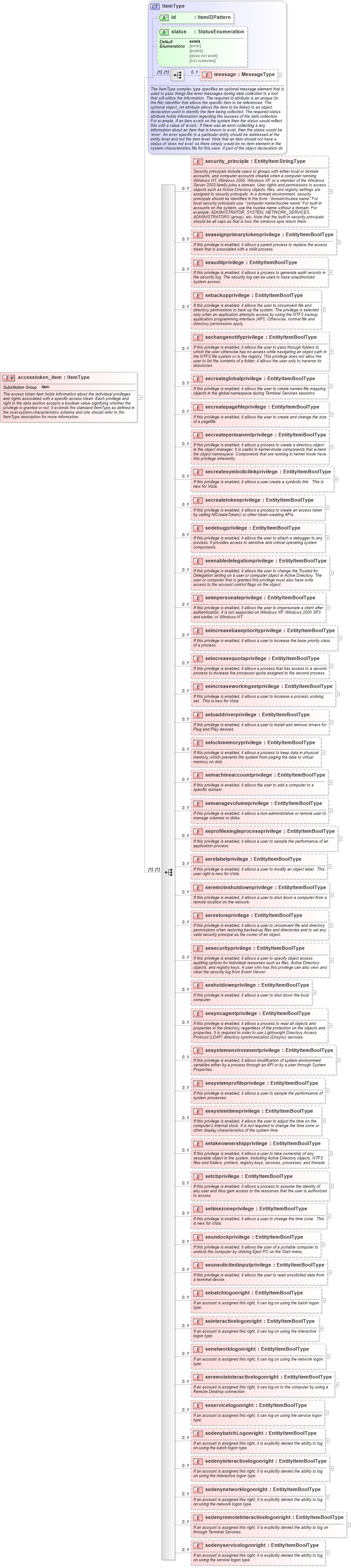
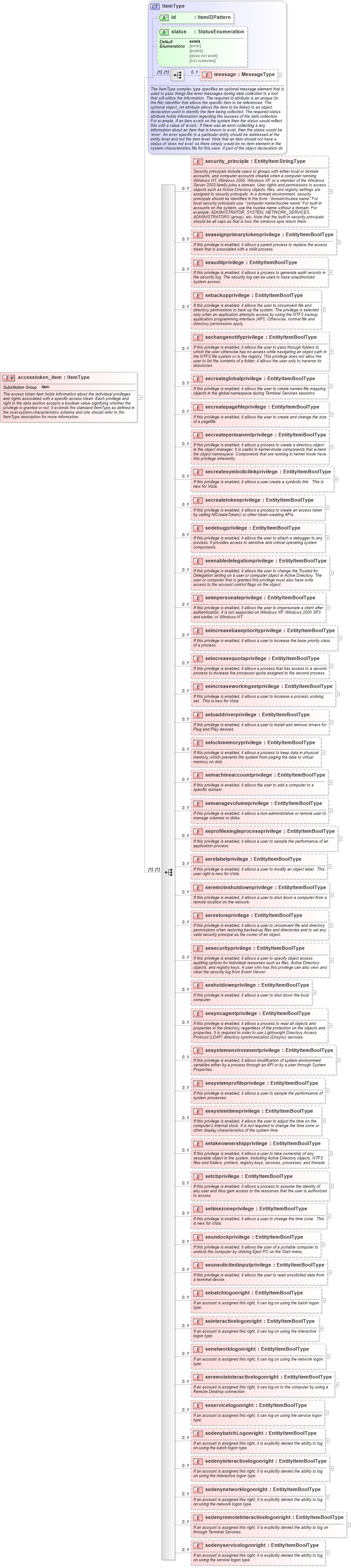
<xsd:element name="accesstoken_item" substitutionGroup="oval-sc:item">
<xsd:annotation>
<xsd:documentation>The access token item holds information about the individual privileges and rights associated with a specific access token. Each privilege and right in the data section accepts a boolean value signifying whether the privilege is granted or not. It extends the standard ItemType as defined in the oval-system-characteristics schema and one should refer to the ItemType description for more information.</xsd:documentation>
</xsd:annotation>
<xsd:complexType>
<xsd:complexContent>
<xsd:extension base="oval-sc:ItemType">
<xsd:sequence>
<xsd:element name="security_principle" type="oval-sc:EntityItemStringType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>Security principals include users or groups with either local or domain accounts, and computer accounts created when a computer running Windows NT, Windows 2000, Windows XP, or a member of the Windows Server 2003 family joins a domain. User rights and permissions to access objects such as Active Directory objects, files, and registry settings are assigned to security principals. In a domain environment, security principals should be identified in the form: "domain\trustee name" For local security principals use: "computer name\trustee name" For built-in accounts on the system, use the trustee name without a domain. For example: ADMINISTRATOR, SYSTEM, NETWORK_SERVICES, ADMINISTRATORS (group), etc. Note that the built-in security principals should be all caps as that is how the windows apis return them.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecurity_principle" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:security_principle">
<sch:assert test="not(@datatype) or @datatype='string'">item <sch:value-of select="../@id" /> - datatype attribute for the security_principle entity of an accesstoken_item should be 'string'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seassignprimarytokenprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a parent process to replace the access token that is associated with a child process.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseassignprimarytokenprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seassignprimarytokenprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seassignprimarytokenprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seauditprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to generate audit records in the security log. The security log can be used to trace unauthorized system access.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseauditprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seauditprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seauditprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sebackupprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to circumvent file and directory permissions to back up the system. The privilege is selected only when an application attempts access by using the NTFS backup application programming interface (API). Otherwise, normal file and directory permissions apply.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsebackupprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sebackupprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sebackupprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sechangenotifyprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to pass through folders to which the user otherwise has no access while navigating an object path in the NTFS file system or in the registry. This privilege does not allow the user to list the contents of a folder; it allows the user only to traverse its directories.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsechangenotifyprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sechangenotifyprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sechangenotifyprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="secreateglobalprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to create named file mapping objects in the global namespace during Terminal Services sessions.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecreateglobalprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:secreateglobalprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the secreateglobalprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="secreatepagefileprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to create and change the size of a pagefile.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecreatepagefileprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:secreatepagefileprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the secreatepagefileprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="secreatepermanentprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to create a directory object in the object manager. It is useful to kernel-mode components that extend the object namespace. Components that are running in kernel mode have this privilege inherently.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecreatepermanentprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:secreatepermanentprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the secreatepermanentprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="secreatesymboliclinkprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user create a symbolic link. This is new for Vista.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecreatesymboliclinkprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:secreatesymboliclinkprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the secreatesymboliclinkprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="secreatetokenprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to create an access token by calling NtCreateToken() or other token-creating APIs.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsecreatetokenprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:secreatetokenprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the secreatetokenprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedebugprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to attach a debugger to any process. It provides access to sensitive and critical operating system components.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedebugprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedebugprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedebugprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seenabledelegationprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to change the Trusted for Delegation setting on a user or computer object in Active Directory. The user or computer that is granted this privilege must also have write access to the account control flags on the object.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseenabledelegationprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seenabledelegationprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seenabledelegationprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seimpersonateprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to impersonate a client after authentication. It is not supported on Windows XP, Windows 2000 SP3 and earlier, or Windows NT.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseimpersonateprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seimpersonateprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seimpersonateprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seincreasebasepriorityprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to increase the base priority class of a process.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseincreasebasepriorityprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seincreasebasepriorityprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seincreasebasepriorityprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seincreasequotaprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process that has access to a second process to increase the processor quota assigned to the second process.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseincreasequotaprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seincreasequotaprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seincreasequotaprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seincreaseworkingsetprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to increase a process working set. This is new for Vista</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseincreaseworkingsetprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seincreaseworkingsetprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seincreaseworkingsetprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seloaddriverprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to install and remove drivers for Plug and Play devices.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseloaddriverprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seloaddriverprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seloaddriverprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="selockmemoryprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to keep data in physical memory, which prevents the system from paging the data to virtual memory on disk.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemselockmemoryprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:selockmemoryprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the selockmemoryprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="semachineaccountprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to add a computer to a specific domain.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsemachineaccountprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:semachineaccountprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the semachineaccountprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="semanagevolumeprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a non-administrative or remote user to manage volumes or disks.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsemanagevolumeprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:semanagevolumeprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the semanagevolumeprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seprofilesingleprocessprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to sample the performance of an application process.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseprofilesingleprocessprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seprofilesingleprocessprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seprofilesingleprocessprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="serelabelprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to modify an object label. This user right is new for Vista.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemserelabelprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:serelabelprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the serelabelprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seremoteshutdownprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to shut down a computer from a remote location on the network.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseremoteshutdownprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seremoteshutdownprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seremoteshutdownprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="serestoreprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to circumvent file and directory permissions when restoring backed-up files and directories and to set any valid security principal as the owner of an object.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemserestoreprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:serestoreprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the serestoreprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sesecurityprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to specify object access auditing options for individual resources such as files, Active Directory objects, and registry keys. A user who has this privilege can also view and clear the security log from Event Viewer.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsesecurityprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sesecurityprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sesecurityprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seshutdownprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to shut down the local computer.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseshutdownprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seshutdownprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seshutdownprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sesyncagentprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to read all objects and properties in the directory, regardless of the protection on the objects and properties. It is required in order to use Lightweight Directory Access Protocol (LDAP) directory synchronization (Dirsync) services.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsesyncagentprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sesyncagentprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sesyncagentprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sesystemenvironmentprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows modification of system environment variables either by a process through an API or by a user through System Properties.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsesystemenvironmentprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sesystemenvironmentprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sesystemenvironmentprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sesystemprofileprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to sample the performance of system processes.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsesystemprofileprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sesystemprofileprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sesystemprofileprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sesystemtimeprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to adjust the time on the computer's internal clock. It is not required to change the time zone or other display characteristics of the system time.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsesystemtimeprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sesystemtimeprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sesystemtimeprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="setakeownershipprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to take ownership of any securable object in the system, including Active Directory objects, NTFS files and folders, printers, registry keys, services, processes, and threads.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsetakeownershipprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:setakeownershipprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the setakeownershipprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="setcbprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a process to assume the identity of any user and thus gain access to the resources that the user is authorized to access.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsetcbprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:setcbprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the setcbprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="setimezoneprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows a user to change the time zone. This is new for Vista.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsetimezoneprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:setimezoneprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the setimezoneprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seundockprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user of a portable computer to undock the computer by clicking Eject PC on the Start menu.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseundockprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seundockprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seundockprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seunsolicitedinputprivilege" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If this privilege is enabled, it allows the user to read unsolicited data from a terminal device.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseunsolicitedinputprivilege" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seunsolicitedinputprivilege">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seunsolicitedinputprivilege entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sebatchlogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it can log on using the batch logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsebatchlogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sebatchlogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sebatchlogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seinteractivelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it can log on using the interactive logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseinteractivelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seinteractivelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seinteractivelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="senetworklogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it can log on using the network logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsenetworklogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:senetworklogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the senetworklogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seremoteinteractivelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it can log on to the computer by using a Remote Desktop connection.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseremoteinteractivelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seremoteinteractivelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seremoteinteractivelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="seservicelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it can log on using the service logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemseservicelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:seservicelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the seservicelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedenybatchLogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it is explicitly denied the ability to log on using the batch logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedenybatchLogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedenybatchLogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedenybatchLogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedenyinteractivelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it is explicitly denied the ability to log on using the interactive logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedenyinteractivelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedenyinteractivelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedenyinteractivelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedenynetworklogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it is explicitly denied the ability to log on using the network logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedenynetworklogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedenynetworklogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedenynetworklogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedenyremoteInteractivelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it is explicitly denied the ability to log on through Terminal Services.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedenyremoteInteractivelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedenyremoteInteractivelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedenyremoteInteractivelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
<xsd:element name="sedenyservicelogonright" type="oval-sc:EntityItemBoolType" minOccurs="0" maxOccurs="1">
<xsd:annotation>
<xsd:documentation>If an account is assigned this right, it is explicitly denied the ability to log on using the service logon type.</xsd:documentation>
<xsd:appinfo>
<sch:pattern id="atitemsedenyservicelogonright" xmlns:sch="http://purl.oclc.org/dsdl/schematron">
<sch:rule context="win-sc:accesstoken_item/win-sc:sedenyservicelogonright">
<sch:assert test="@datatype='boolean'">item <sch:value-of select="../@id" /> - datatype attribute for the sedenyservicelogonright entity of an accesstoken_item should be 'boolean'</sch:assert>
</sch:rule>
</sch:pattern>
</xsd:appinfo>
</xsd:annotation>
</xsd:element>
</xsd:sequence>
</xsd:extension>
</xsd:complexContent>
</xsd:complexType>
</xsd:element>
|